Unveiling Cybersecurity: Navigating the OWASP Top 10 with Appsealing
Introduction
In an age dominated by technological advancement, the complexities and vulnerabilities of cybersecurity are crucial to the success of business and customer information. The cyber threat environment continues to change and calls for proactive measures to shield digital assets from potential openings. An important step in this path is recognizing OWASP Top 10 and using the most contemporary technology in application security for example Appsealing.
Unmasking the OWASP Top 10
OWASP Top 10 is a collection of the top ten vulnerabilities within web applications. Cybersecurity professionals have thoroughly mapped these risks, which serve as a guide for developers, security professionals, and organizations toward better-securing web applications.
The Dynamic Nature of Threats
Malicious actors adopt increasingly advanced strategies as technology develops. OWASP Top 10 is a “living document” that periodically gets updated to cover emerging threats. This is an ongoing process and each new iteration is a reminder of the importance of constant alertness in cyberspace.
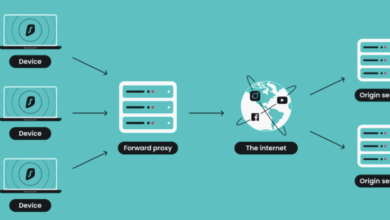
A Closer Look at Appsealing
Appsealing is a new invention that helps to make mobile applications stronger in response to threats. AppSealing is a full-suite mobile app security solution that protects against unauthorized access, data breaches, and tampering. Let’s take a look at the way this advanced technology applies to the OWASP Top 10.
Keyword Encryption: Guarding Against Injection Attacks
Injection attacks are permanent fixtures in the OWASP top ten and exploit weaknesses in data entry channels. To combat this threat, appsealing offers for keyword encryption. It is the approach where sensitive keywords are obscured making it extremely difficult for the attacker to inject input fields into web pages and execute malware.
Dynamic Code Protection: Taming Broken Authentication
These involve authentication vulnerabilities, which commonly occur due to vulnerabilities associated with broken authentication mechanisms. Dynamic code protection is a new complex measure provided by app sealing, which modifies the original structure of an app’s code on the fly during operations. This makes this approach a new shield in the attempt to break the conventional attack vectors used in unauthorized access.
Secure communication as shielding sensitive data
One common concern, especially in this era of connected applications, is data exposure. The appsealing places emphasis on secure communication which employs strong encryption algorithms. The application transmits the sensitive data to the server in an encrypted form through the SSL protocol, thus minimizing the chances of exposure and unauthorized access to that data.
Runtime Application Self-Protection (RASP): A Guardian Against Security Misconfiguration
As illustrated in the OWASP Top 10, security misconfigurations can have dramatic repercussions. In their turn, the appsealing technology incorporates runtime application self-protection (RASP), allowing the application to detect and react to security irregularities dynamically. This “virtual guardian” is an adaptive defense mechanism that lessens the consequences of misconfigurations in real-time.
The Collaborative Synergy: OWASP Top 10 and Appsealing
Although the OWASP top 10 lists act as the framework for identifying and prioritizing security vulnerabilities, appsealing is the dynamic implementation of these principles. These unite to form a powerful alliance that makes mobile applications stronger and sets new benchmarks in adaptability during the increasing cyber threats.
Continuous Evolution and Adaptation
However, this relationship between AppSealing and OWASP Top 10 has a dynamism. It reflects the endless growth in the cybersecurity world. Both companies adjust as new threats arise, and the protection systems remain strong despite the changing tactics of the cyber adversaries.
Empowering Developers Through Knowledge
OWASP Top 10 provides a deep understanding of the application vulnerabilities and enables developers to harden the applications right at their core. This knowledge on OWASP top 10 is augmented by Appsealing which is a practical and usable remedy that matches with the OWASP Top 10. This helps developers design robust applications that can withstand different types of cyber attacks.
Behavioral Analysis for Anomaly Detection
Proactive measures in cybersecurity. AppSealing also uses behavior analysis to detect abnormalities in how users engage with applications and application behavior. This is another level of deterrence, which constantly monitors patterns and deviations to identify potential threats and contain them before they escalate into emerging risks.
Code Tampering Resistance
Attackers keep searching for ways of messing around with the application code to gain unauthorized entry or add malicious elements. Appsealing ensures that applications are protected against such tampering through code integrity checks in addition to real-time monitoring. Any changes that are unauthorized lead to responses immediately, hence denying exploitation of vulnerabilities created by code tampering.
Secure Key Storage and Management
The strength of encryption depends on the management of cryptographic keys. With appsealing, encrypted keys are kept safe, blocking any efforts to interfere or hack into any sensitive information. This third level of security strengthens the confidentiality and integrity of data by using industry-best practices in key management, addressing critical issues of the OWASP Top 10.
Runtime Threat Intelligence Integration
Real-time intelligence on impending threats is needed to be on the front foot. Appsealing combines runtime threat intelligence, ensuring that applications are updated with knowledge of prevalent vulnerabilities and common attack patterns. This, therefore, makes the organization’s security posture adjustable and capable of preventing attacks and other risks that do not form part of the OWASP Top 10.
User Authentication Enhancements
Application security requires proper authentication; Appsealing improves on that through its multiple authentication layers. Authentication processes encompass biometrics, device fingerprinting, behavioral analysis, and more advanced username-password combinations beyond the conventional ones. This complex approach helps prevent unauthorized access, tackling issues raised by the OWASP Top 10 about broken authentication.
Strengthening Integrity: Code Whitelisting Mechanisms
Therefore, code integrity is essential in protecting applications against malicious modifications. Appsealing applies enhanced code white lists, whereby only vetted and legitimate code is allowed to run. This layer of defense meticulously controls the execution of code within the application environment thereby preventing injection of unauthorized code or manipulation. The measures help to block several attacks that may otherwise compromise the OWASP Top 10.
Conclusion: A Secure Tomorrow
In our digital world, the intersection of OWASP Top 10 and advanced technologies like Appsealing marks the dawn of a secure tomorrow. The struggle against cybercrime continues, yet knowledge and technological breakthroughs empower us to improve our digital infrastructure to preserve the applications that are vital to us today. Let us unite in a future where cyber security is not a prerequisite but a shared duty in the universe of unlimited opportunities on the web.