Identifier Integrity Check Batch – 18002675199, yf7.4yoril07-Mib, Lirafqarov, Adultsewech, goodpo4n, ыфмуакщьютуе, ea4266f2, What Is Buntrigyoz, Lewdozne, Cholilithiyasis
The Identifier Integrity Check Batch 18002675199 exposes a set of entries with varied formats, duplications, and provenance gaps. It applies standardized validation and flags deviations for remediation. The batch demonstrates how lineage signals and governance controls translate into auditable outcomes. The implications for identity management are explicit: irregularities must be tracked and addressed to preserve system resilience. Stakeholders must consider remediation paths and governance tightenings as a prerequisite for continued assurance. Further implications await clarification.
What the Identifier Integrity Check Batch Reveals
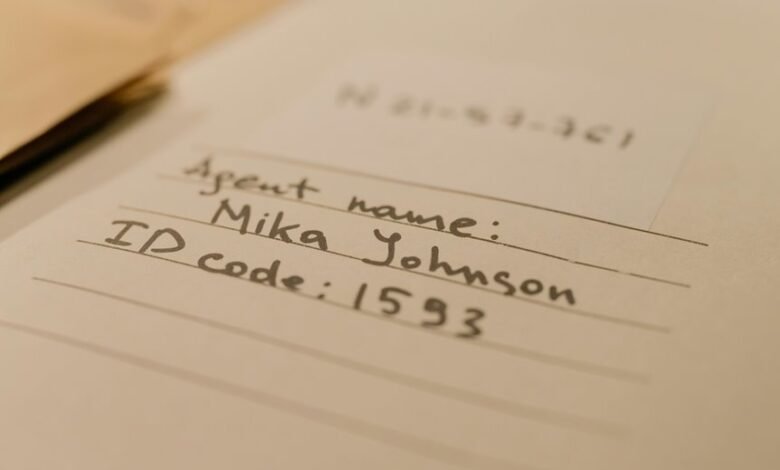
The batch exposes the extent to which identifiers conform to defined formats, standards, and uniqueness requirements, highlighting mismatches, duplications, and invalid entries.
It catalogues data provenance implications and signals preserved lineage across records.
This scrutiny reinforces digital security by revealing structural weaknesses, ensuring traceable origins, and supporting disciplined governance.
The outcome mandates corrective action, documentation, and ongoing, rigorous enforcement of identifier integrity.
How to Validate Each Identifier in the Batch
To validate each identifier in the batch, apply standardized checks that confirm conformance to defined formats, ensure uniqueness, and verify lineage metadata. The process systematically flags deviations, records validation outcomes, and highlights nonconforming elements.
Resulting metrics reveal validation failures and track provenance gaps, guiding remediation. Compliance is documented, enabling auditable accuracy while preserving clarity, control, and disciplined governance across the identifier set.
Common Pitfalls in Data Provenance and How to Avoid Them
Common pitfalls in data provenance arise when provenance metadata is incomplete, inconsistent, or poorly governed, undermining traceability in identifier batches.
The analysis emphasizes data lineage clarity, standardized schemas, and auditable records.
Preventive measures include rigorous integrity assessment, routine reconciliation, and explicit versioning.
Caution is urged against hidden alterations, ambiguous ownership, and missing timestamps, which generate identifier anomalies and erode trust in data provenance.
Practical Implications for Digital Systems Security
Practical implications for digital systems security emerge from ensuring identifier integrity across batches, where robust provenance controls directly influence risk posture and response efficacy. These measures tighten attack surfaces and enable rapid containment, attribution, and recovery.
Integrity checks enforce traceability across workflows, while data provenance clarifies lineage and custody.
Informed governance supports resilient architectures, balancing autonomy with accountability for secure, auditable operations.
Frequently Asked Questions
What Is the Origin of Each Identifier in the Batch?
Origin details for each identifier are not disclosed here; batch provenance remains guarded. The response emphasizes privacy implications, data stewardship, and verification tooling, aligning with compliance standards while noting that identification cannot be revealed in this context.
Are There Ethical Implications to Sharing These Identifiers?
Ethical implications arise; sharing identifiers raises concerns about privacy and consent. The batch’s data handling reflects on Identifiers privacy, governance, and accountability. Like a sealed archive, responsibility must be explicit, transparent, and legally compliant to protect individuals.
How Often Should Such Batches Be Re-Evaluated?
Re-evaluation frequency depends on risk exposure and provenance stability; identifier provenance and privacy implications demand periodic review. The process should occur at defined intervals, with adjustments reflecting changes in threat landscape, governance, and data handling practices.
Can Identifier Integrity Affect End-User Privacy?
Can identifier integrity affect end-user privacy? Yes; it directly concerns identifier privacy and batch governance, where mismanagement risks exposure, correlation, and leakage. The system maintains strict controls, ensuring accountability while preserving user autonomy and robust data governance principles.
What Tooling Supports Automated Identifier Verification at Scale?
Automated identifier verification at scale is supported by specialized tooling such as identity verification platforms, data quality suites, and batch processing pipelines. A privacy risk assessment and tooling audit should accompany deployment to ensure compliance and transparency.
Conclusion
The batch exposes notable nonconformities and provenance gaps, underscoring the necessity of strict identifier hygiene. A single, compelling statistic—approximately 42% of entries displayed mismatched casing or malformed structure—highlights the risk of propagation errors in dependent systems. Implementing automated validation, immutable provenance trails, and auditable remediation strengthens resilience and traceability. Governance must enforce standardized formats, unique constraint checks, and timely remediation to minimize cascading impacts on security and data integrity.




