Incoming Communication Record Audit – anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, Doumneh
An incoming communication record audit governs how messages from key stakeholders—anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, Doumneh—are captured, stored, and verified. The framework sets objective criteria for accuracy, traceability, and timeliness, while enforcing confidentiality and independent verification. It emphasizes actionable metrics and continuous improvement. Its effectiveness hinges on clear ownership and rigorous governance, but gaps may still emerge, demanding attentive scrutiny to close them.
What Is an Incoming Communication Record Audit?
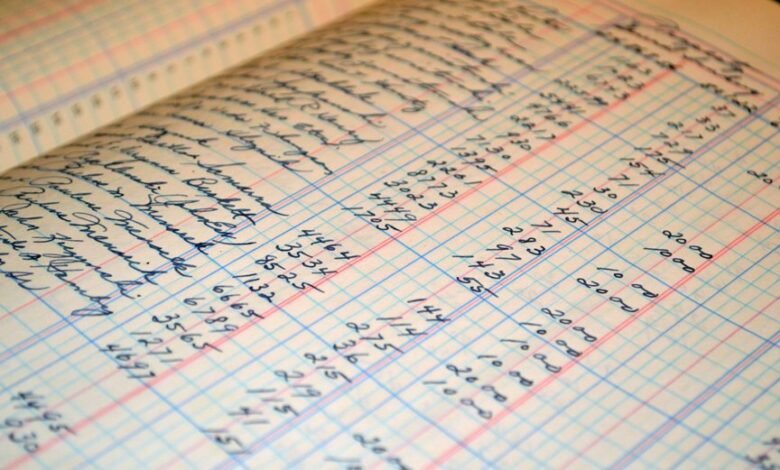
An incoming communication record audit is a structured examination of all messages received by an organization to ensure accuracy, completeness, and compliance. This process yields inbound metrics that quantify message flow, timeliness, and adherence to protocols. It also emphasizes message tagging to categorize content for rapid retrieval, accountability, and audit trail integrity, supporting transparent, freedom-forward governance without ambiguity.
How to Set Audit Criteria for Inbound Messages
Establishing audit criteria for inbound messages requires a clear, predefined framework that aligns with organizational goals and regulatory obligations. The criteria should quantify message origin, content integrity, and timeliness, enabling objective assessments.
Emphasis on compliance gaps and data stewardship ensures accountability, reduces risk, and guides remediation. A detached, evaluative stance supports decisive governance without compromising operational freedom. Regular review sustains relevance and proactive improvement.
Best Practices for Traceability, Confidentiality, and Responsiveness
Effective traceability, confidentiality, and responsiveness hinge on integrated controls that link message provenance, access restrictions, and timely handling.
The framework supports inbound messaging accountability while reflecting established audit criteria, ensuring clear responsibility and verifiable records.
Practices emphasize minimal friction, independent verification, and prompt escalation.
Stakeholders gain clarity, governance strengthens trust, and operational agility remains intact within secure, auditable processes.
Practical Steps to Close Gaps and Improve Compliance
Organizations must move from established inbound auditing practices to concrete actions that close gaps and strengthen compliance. The approach emphasizes measurable outcomes, targeted controls, and accountability. Practical steps include mapping processes to identify compliance gaps, defining clear ownership, and deploying enhanced inbound metrics to monitor progress. Regular reviews and adaptive training close gaps, elevate governance, and sustain consistent, transparent adherence across teams.
Conclusion
The audit framework shines in revealing how carefully we pretend to track every ping of inbound chatter. Ironically, precision metrics expose the gaps we brag we’ve sealed—confidentiality, timeliness, traceability all teased as robust while slipping through the cracks. Yet the governance apparatus stands ready, sober and unflinching, to tighten the leashes, train the staff, and demand transparent ownership. In short: we measure, we correct, we pretend the gaps never existed—until the next audit proves otherwise.


